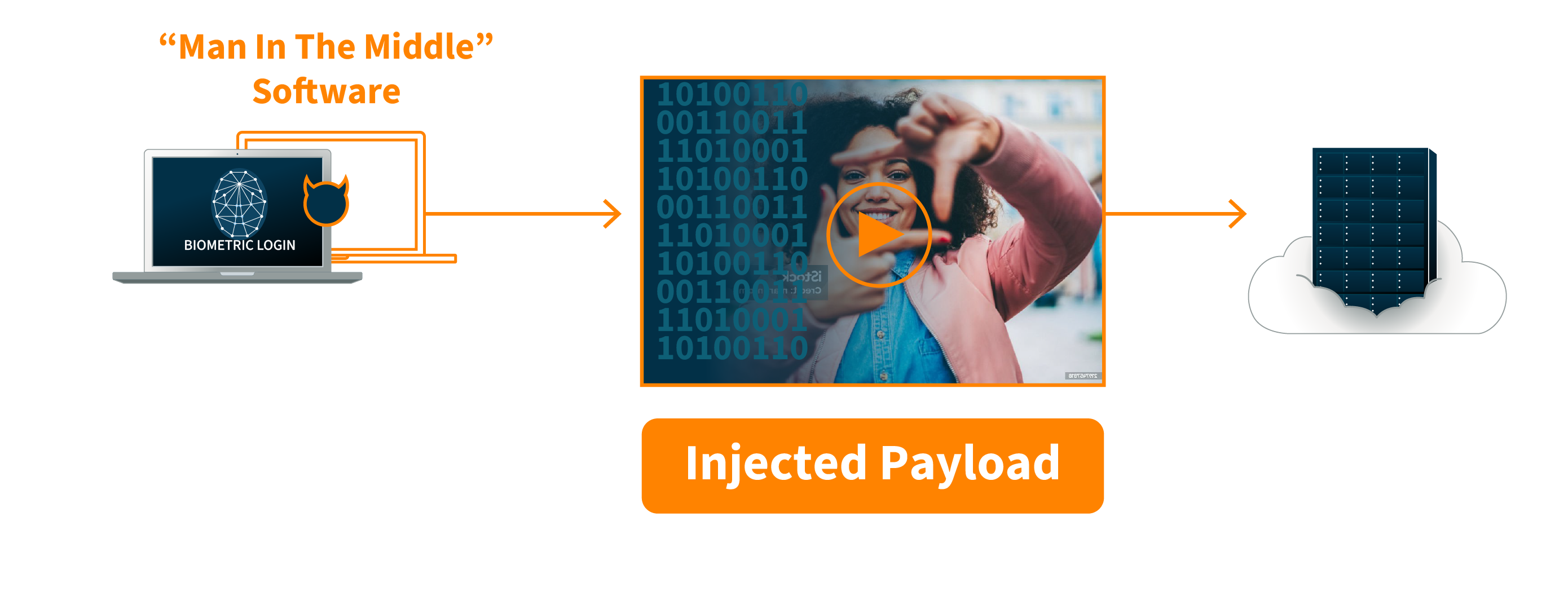
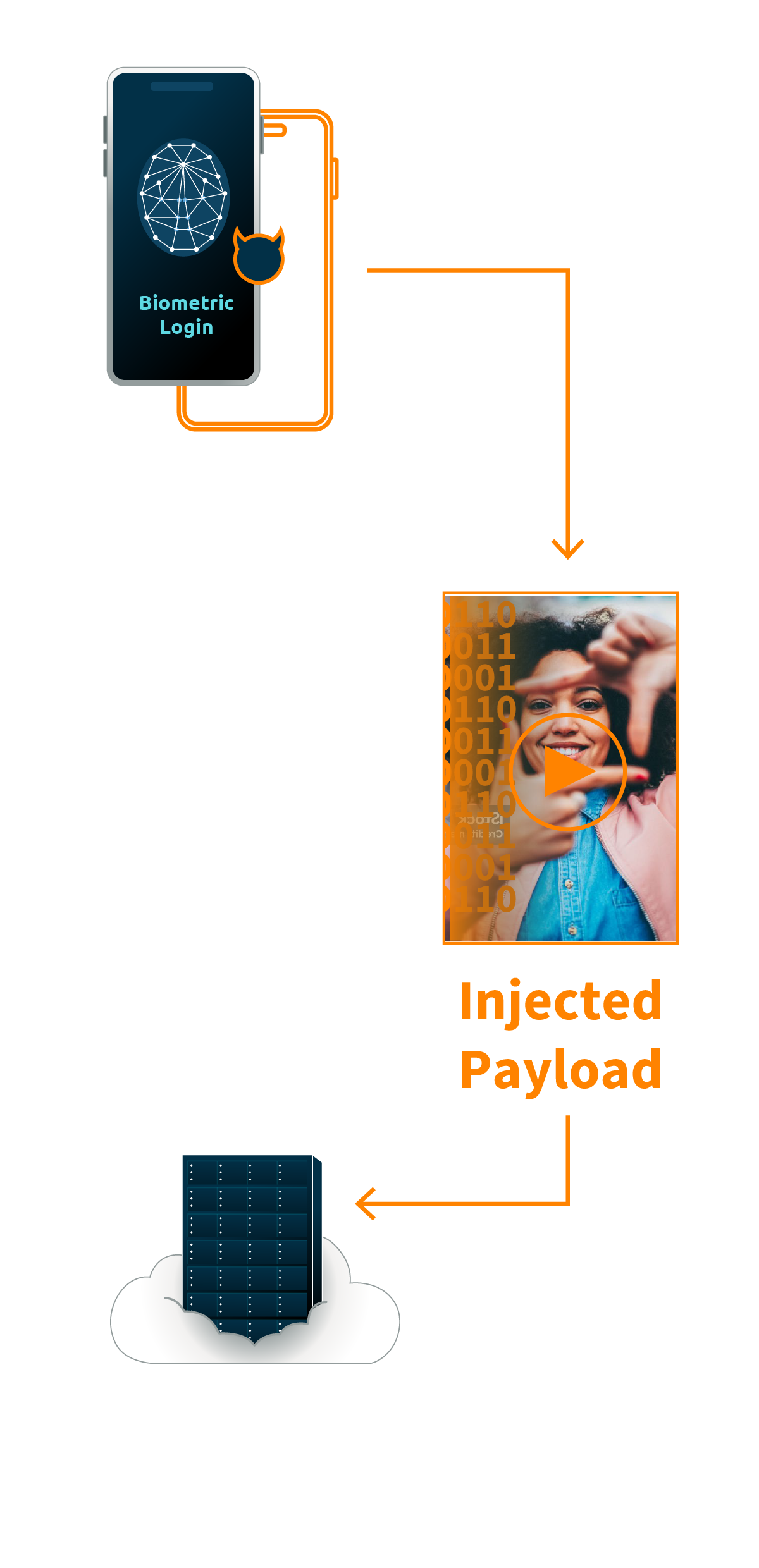
Targeting the User Image
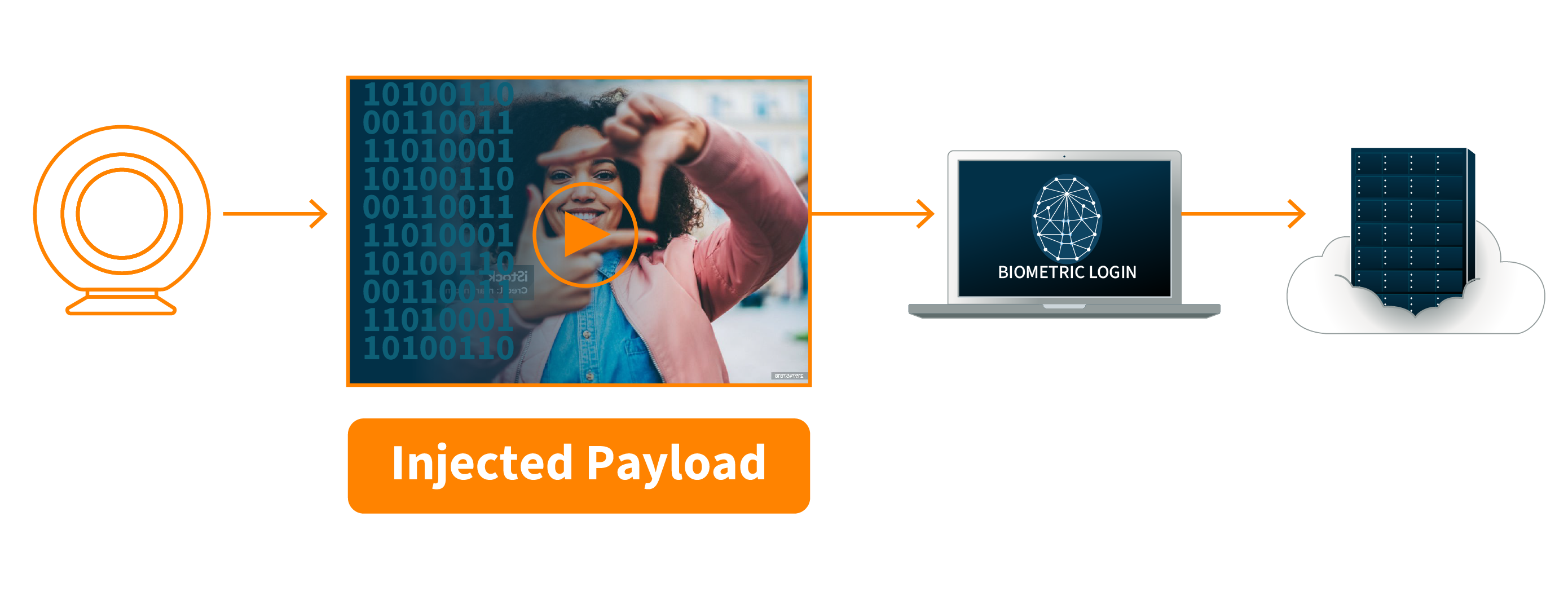
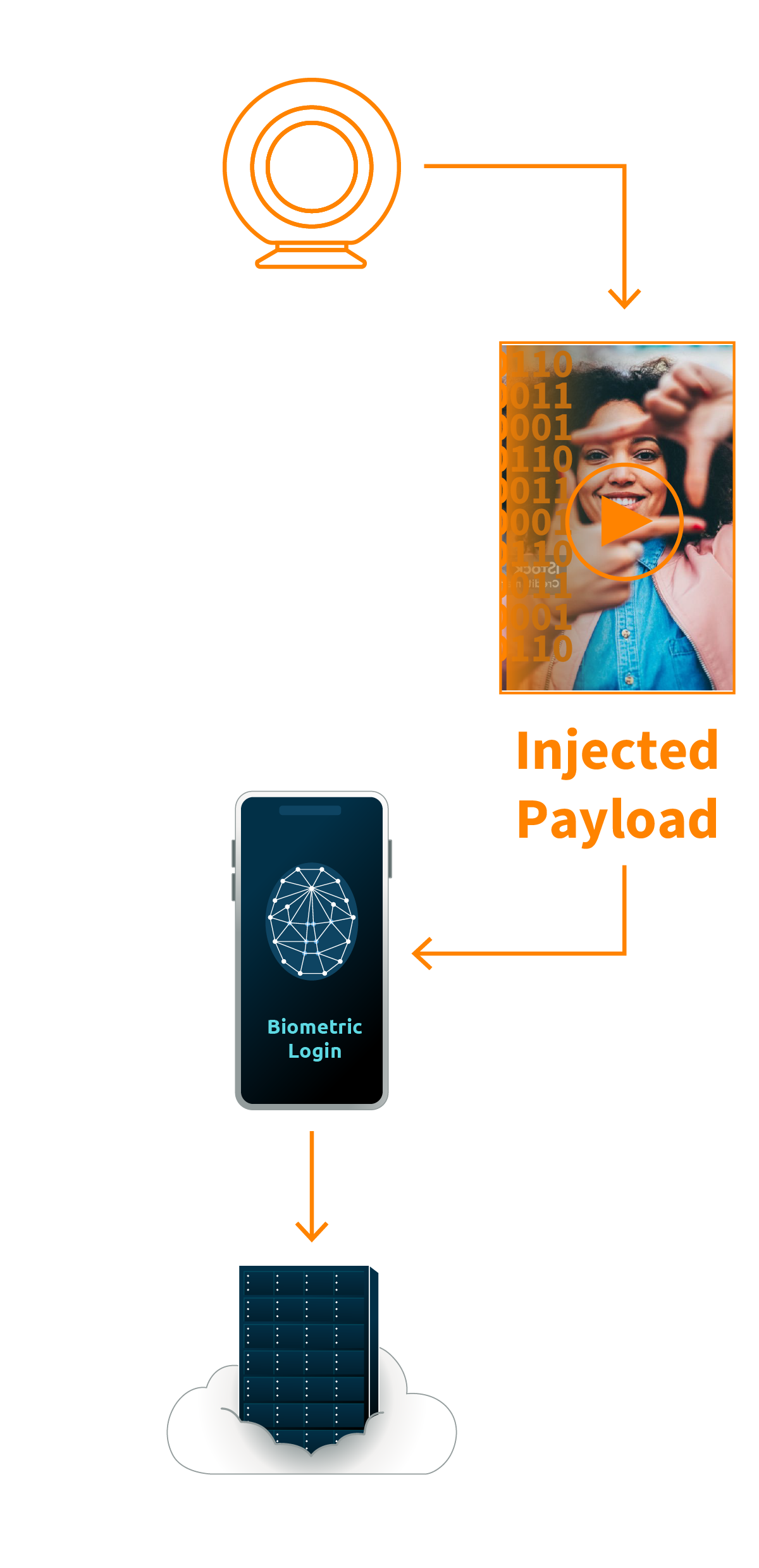
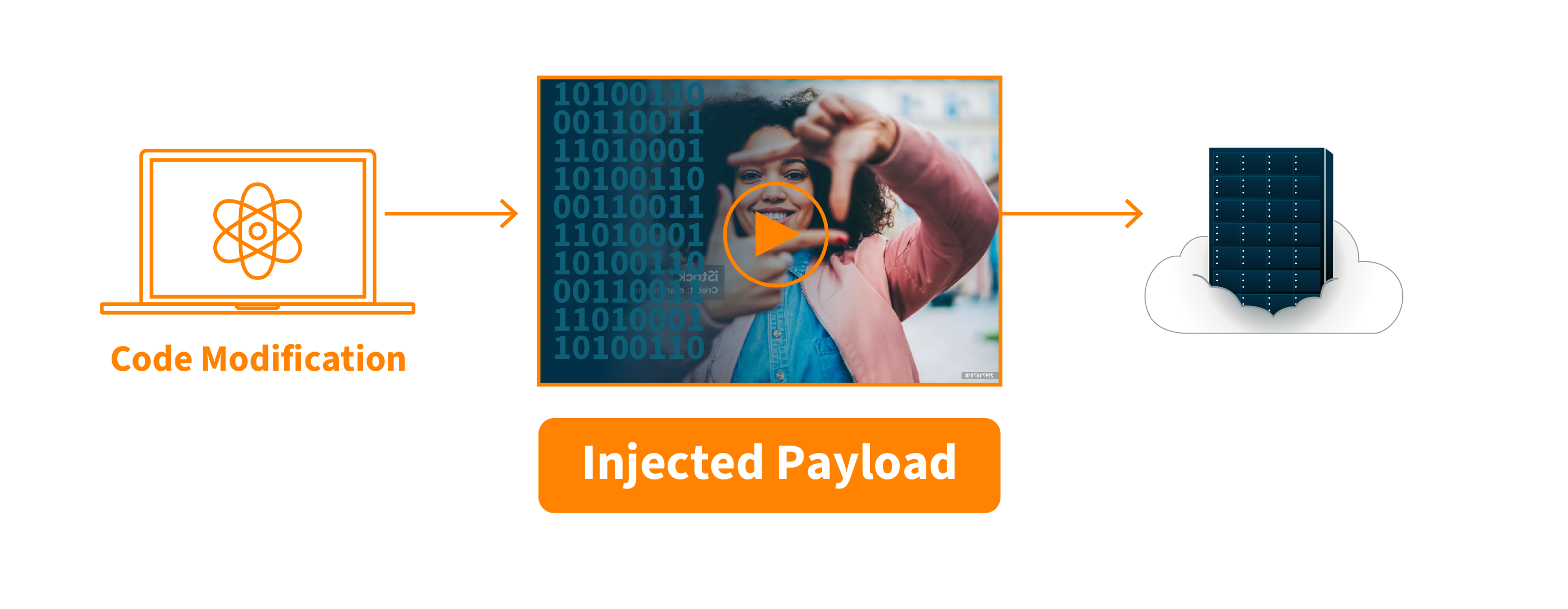
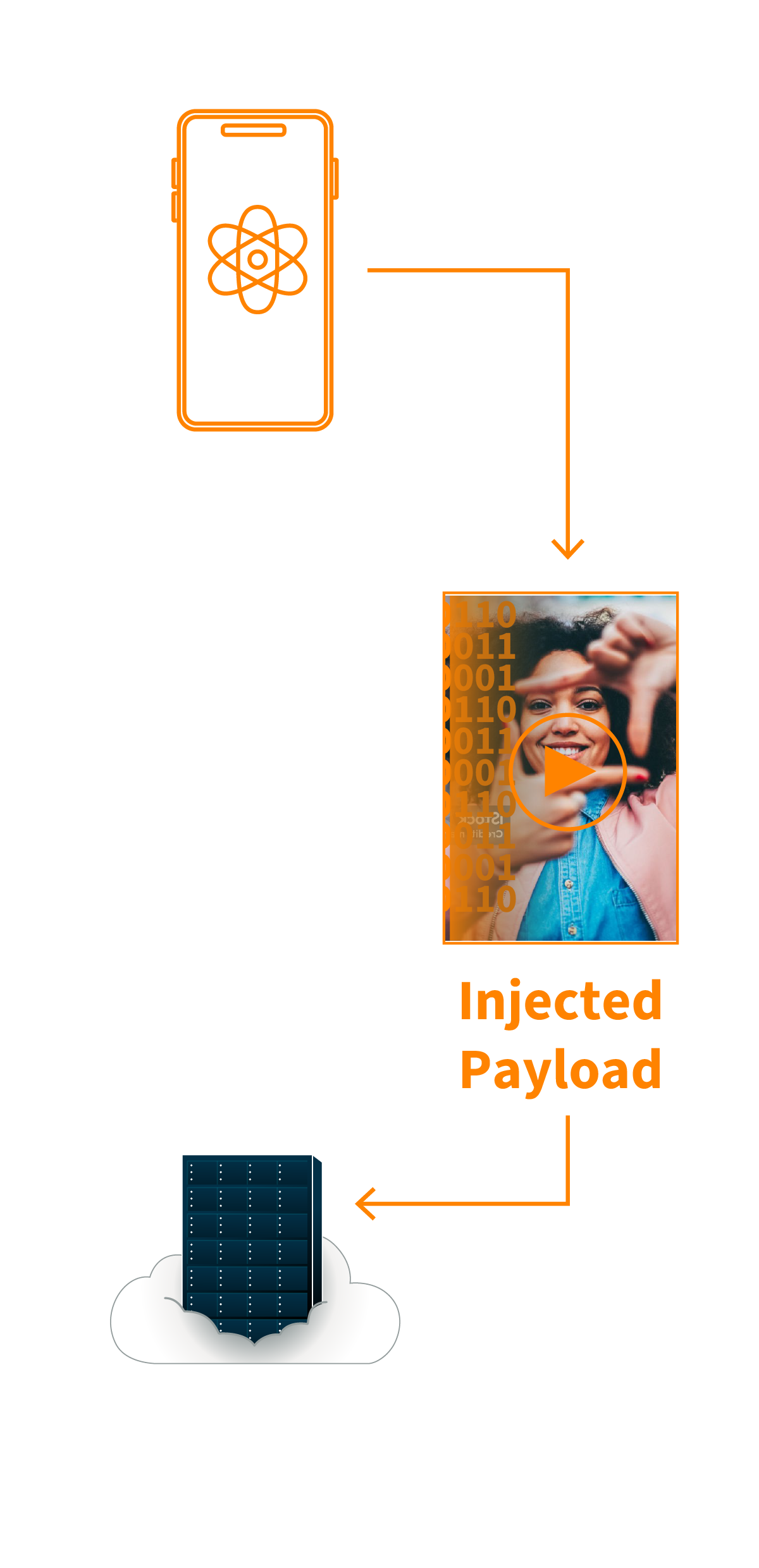
Presentation Attacks
A presentation attack occurs when the user presents a physical spoof between themselves and the camera. These are easily detected by modern systems, but still must be acknowledged.
Types of presentation attacks include: