Anatomie eines Identitätsangriffs
Generative KI ist der Treibstoff für die nächste Generation des Identitätsbetrugs
Um ihren Schutz zu verstärken, setzen viele Unternehmen auf die biometrische Gesichtsverifikation als hochsichere und einfach zu handhabende Methode zur Identitätssicherung, um Benutzer einzubinden und neu zu authentifizieren.
Die Identitätskrise erklärt
Künstliche Intelligenz birgt ein enormes Potenzial - aber sie wird auch als Waffe eingesetzt, um eine globale Identitätskrise zu verursachen. Hochentwickelte synthetische Medien untergraben das Vertrauen in Regierungen, Unternehmen und Menschen.
Die Landschaft der biometrischen Bedrohungen hat sich grundlegend verändert. Was früher ein hohes Maß an technischem Know-how erforderte, ist heute durch einfach zu bedienende Tools, Marktplätze und Anleitungen möglich. Diese Demokratisierung der Angriffsmöglichkeiten hat zu einem explosionsartigen Anstieg von Umfang und Reichweite geführt. Aber auch böswillige Akteure machen sich innovative Technologien zunutze und nutzen zunehmend generative KI, um immer raffiniertere Methoden zu entwickeln, um Betrug zu begehen, Geld zu waschen oder andere illegale Aktivitäten zur finanziellen Bereicherung zu begehen. Leider sind die meisten biometrischen Lösungen zwar gegen Präsentationsangriffe gewappnet, aber viele haben Probleme, sich gegen die viel einfacher zu erstellenden und skalierbaren digitalen Injektionsangriffe wie Deepfakes zu schützen, Gesichtsvertauschungenund sogar synthetische Identitäten.
Um Unternehmen dabei zu helfen, die Anatomie eines Identitätsangriffs besser zu verstehen, stellt iProov Erkenntnisse aus seinem Security Operations Center (iSOC) zur Verfügung. iSOC nutzt hochmoderne Computer-Vision-Systeme mit maschinellem Lernen in Verbindung mit ergänzenden, multimodalen Ansätzen, um biometrische Angriffsmuster über mehrere Regionen, Geräte und Plattformen hinweg zu erkennen.
iSOC Kriminelle heben digitale Injektionsangriffe auf ein neues Niveau:
- Bedrohungsakteure führen digitale Injektionsangriffe plattformübergreifend durch und zielen auf das mobile Web, das native Android und das native iOS über Emulatoren ab.
- Das Aufkommen und die Zunahme von ausgeklügelten Gesichtstausche und synthetische Identitäten lässt vermuten, dass Kriminelle mit geringen Kenntnissen nun über die Mittel verfügen, um fortgeschrittene Angriffe zu starten.
- Bedrohungsakteure führen bewegungsbasierte Angriffe gleichzeitig und in großem Umfang gegen Hunderte von Systemen auf der ganzen Welt durch.
Das Verständnis und die Aufdeckung der Anatomie eines Identitätsangriffs sind von entscheidender Bedeutung für die Auswahl der biometrischen Lösungen, die für die Anforderungen Ihres Unternehmens am besten geeignet sind.
Lesen Sie weiter, um mehr über die biometrische Bedrohungslandschaft zu erfahren, die Verhaltenstrends von Bedrohungsakteuren zu entdecken und zu verstehen, warum nicht alle biometrischen Technologien gleich sind, wenn es um diese Bedrohungen geht.
Anatomie eines Identitätsangriffs Statistik
Prognostizierte Verluste durch synthetischen Identitätsbetrug (SIF) bis 2030
Bedrohungsdaten und Einblicke von Andrew Newell, Chief Scientific Officer
Biometrische Angriffsarten verstehen
Präsentation Angriffe
Die Angreifer verwenden Fotos, Masken oder synthetische Medien vor einer Kamera. PAD-akkreditierte Lösungen fangen viele ab, aber KI-Bilder machen diese Fälschungen viel überzeugender.
Digitale Injektionsangriffe
Eine viel größere Bedrohung: das Einspeisen synthetischer Medien direkt in den Datenstrom. Diese Angriffe:
- Unbegrenzt skalieren
- keine physische Anwesenheit erfordern
- Ende 2022 sind die Angriffe auf die Präsentation 10:1 in der Überzahl
Übliche Angriffstechniken
Synthetischer Identitätsbetrug (SIF)
- Mischt echte und gefälschte Daten
- GANs erzeugen realistische Gesichter
- Baut mit der Zeit Vertrauen auf, was die Entdeckung erschwert
- Bis 2030 werden Kosten in Höhe von 23 Milliarden Dollar prognostiziert
Gesichtstausch
- Überlagerung echter biometrischer Daten mit Bildern von Angreifern
- Übernahme von Konten ermöglichen
- Anstieg um 300% im Jahr 2024
Bild-zu-Video-Konvertierung
- Verwandelt Standfotos in realistische Videos
- Vereinfacht die Erstellung synthetischer Identitäten
- Umgehung grundlegender Lebensdauerkontrollen
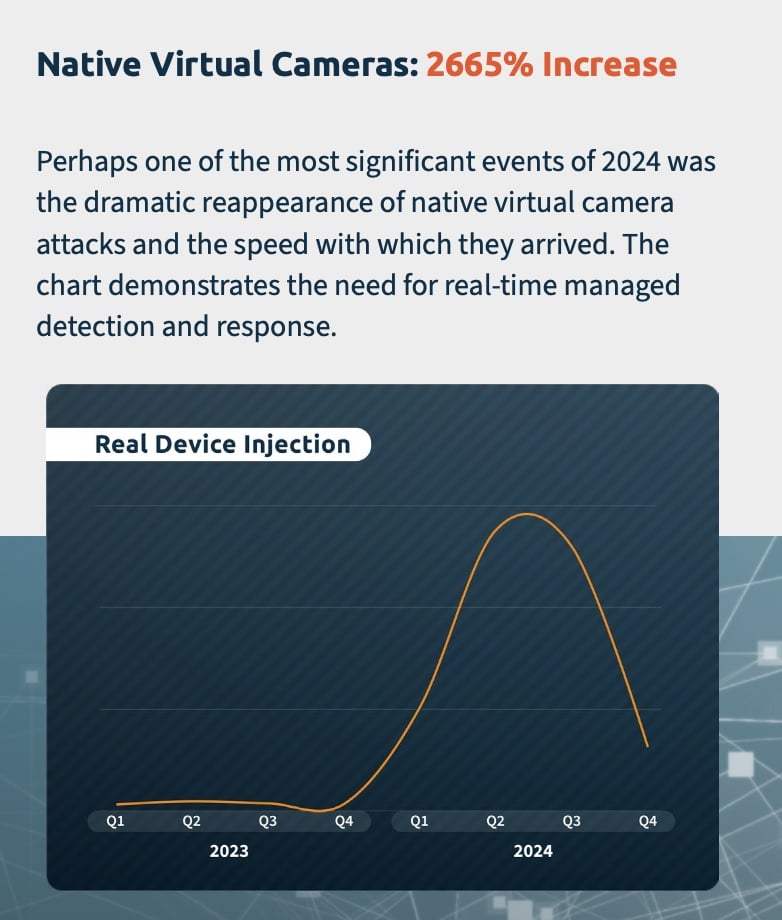
Native Angriffe mit virtueller Kamera
- Direktes Einfügen von AI oder voraufgezeichnetem Filmmaterial
- 2665% Anstieg im Jahr 2024
- Mainstream-Apps machten diese Tools weithin verfügbar
Crime-as-a-Service
- Dark Web Kits + Tutorials für Nicht-Experten
- 31+ neue Bedrohungsgruppen im Jahr 2024 identifiziert
Das Versagen der menschlichen Erkennung
- Nur 0,1 % der Menschen erkannten alle synthetischen Beispiele
- Geschulte Profis erreichten nur 50 % Genauigkeit
- Die Überprüfung durch menschliche Bediener wird umgangen
- Selbstüberschätzung führt zu kostspieligen Fehltritten
Kannst du einen Deepfake erkennen? Machen Sie den Deepfake-Erkennungstest!
Die finanziellen Auswirkungen
- 8,8 Milliarden Dollar an Identitätsverlusten (2023)
- Betrugsverluste in Höhe von 10,2 Mrd. Dollar (H1 2024)
- Durchschnittlich 4,24 Millionen Dollar pro Sicherheitsvorfall
- 25,6 Millionen Dollar bei einem einzigen Deepfake-Betrug verloren (Hongkong)
Ist Ihre aktuelle Lösung Deepfake-fähig?
Der Markt ist überschwemmt mit Anbietern von Liveness-Lösungen, die behaupten, vor Fälschungen zu schützen und mühelos nutzbar zu sein, was oft nicht bewiesen ist. Dies macht die Auswahl des richtigen Anbieters zu einer Herausforderung.
Machen Sie unser 2-minütiges Liveness Assessment, um Ihre Sicherheit gegen KI-Bedrohungen zu bewerten.
Gewinnen Sie wertvolle Einblicke in die Leistung Ihres Liveness-Anbieters und decken Sie kritische Bereiche wie Angriffserkennung, Sicherheitsupdates, Benutzerfreundlichkeit, Zugänglichkeit, Kunden- und Partnersupport und Governance ab.

ZERTIFIZIERUNGEN SIND WICHTIG.
- eIDAS Zuverlässigkeitsgrad Hoch
- ISO/IEC 30107-3
- SOC 2 Typ II
- UK Government Digital Identity and Attributes Trust Framework Zertifizierung
- Zertifizierter G-Cloud-Anbieter
- Federal Reserve SIF Mitigation Provider
- iBeta
- iRAP
- UK Nationales Physikalisches Laboratorium (NPL)
AnatOmie eines Identitätsangriffs RESOURCE LIBRARY
In unserer Ressourcenbibliothek finden Sie Artikel, Fallstudien, Berichte, Pressemitteilungen und vieles mehr.