January 25, 2023
Data privacy is critical to the biometric ecosystem. But why, exactly, does it matter?
- Because traditional authentication methods are no longer enough to protect personal data: Fraud grows, both in scale and complexity as consumers and organizations move transactions increasingly online. Passwords and other traditional verification methods are no longer fit for purpose – they’ve become a well-known commodity to cybercriminals. Biometric security is necessary to protect users from the threat of data breaches, compromised credentials, and more.
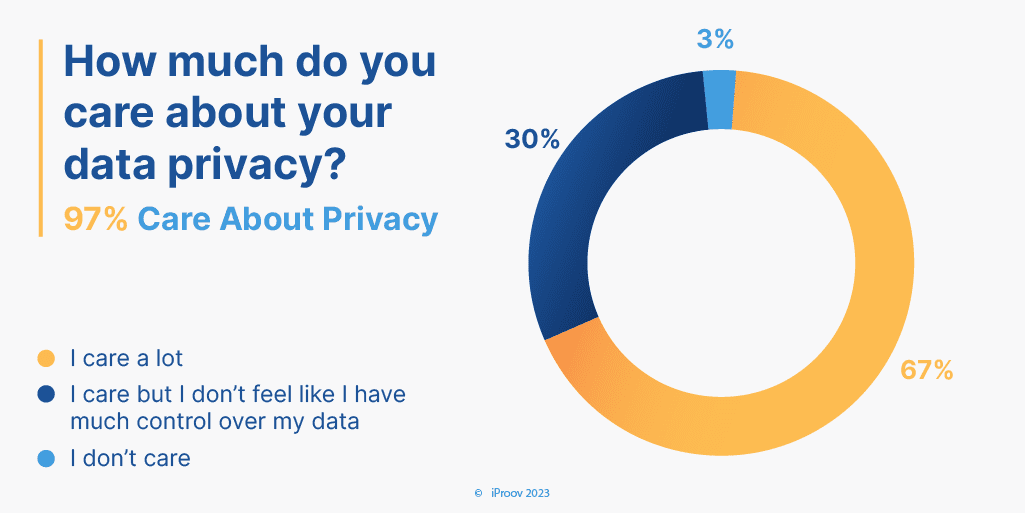
- Because consumers care: iProov research finds that an overwhelming majority (97%) of consumers care about the privacy of their data and how their data is used.
- Because it is the law: GDPR and the UK Data Protection Act, for example, are enforced by regulators, such as the UK’s Information Commissioner’s Office (ICO). In many contexts biometric data is classed as special category data, affording it extra protections.
Protection of user data is built into iProov’s very design. When you procure iProov, you are procuring a technology that maximizes privacy protection, as highlighted by our conformance with many stringent security and privacy standards.
Next, we’ll answer a few questions about data privacy using our original research.
How Many People Care About Data Privacy?
It’s been suggested that the average person today has over 100 online accounts. Does this mean that consumers are relaxed about sharing data? Not quite – consumers are concerned about privacy:
- In total, 97% of consumers care about data privacy.
- The majority of global consumers (68%) “care a lot” about data privacy.
- 30% care about data privacy but feel they do have much control over it.
Here are the results breakdown by country:
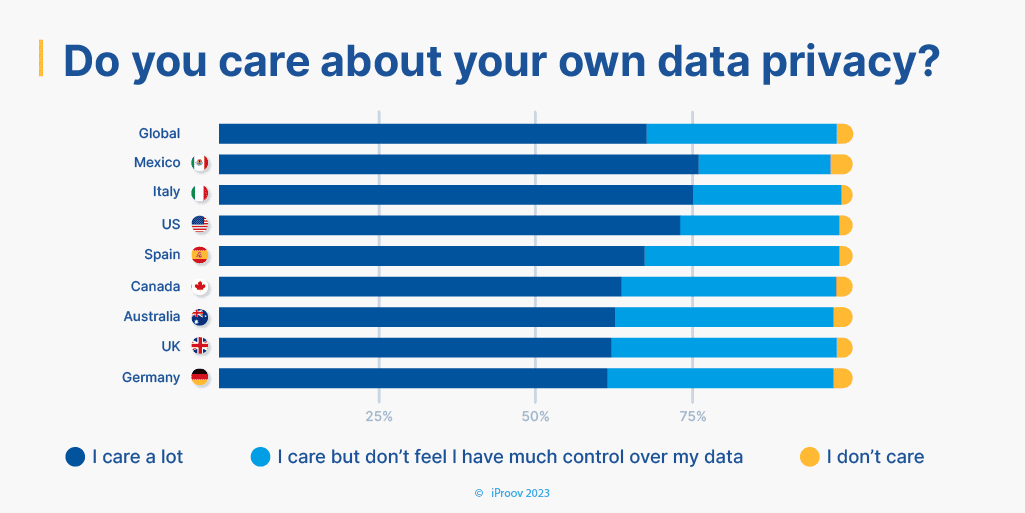
Clearly, consumers want control of their data. This could mean two things:
- Consumers are more likely to avoid services that ask for too much information to be shared.
- Consumers are more likely to avoid services that do not take data privacy seriously.
It’s interesting to see how attitudes have changed over time here. We asked consumers the same question in 2020; 25% of respondents “cared”, but did not feel they had much control over their data. In 2023, it’s up to 30% – indicating that consumers feel they are gradually losing control of data.
What Puts Data Privacy at Risk?
Aside from their inconvenience, the problem is that knowledge-based security (like passwords) can be shared, lost, guessed, and stolen. 80% of hacking-related breaches involve compromised and weak credentials. This puts data privacy at significant risk.
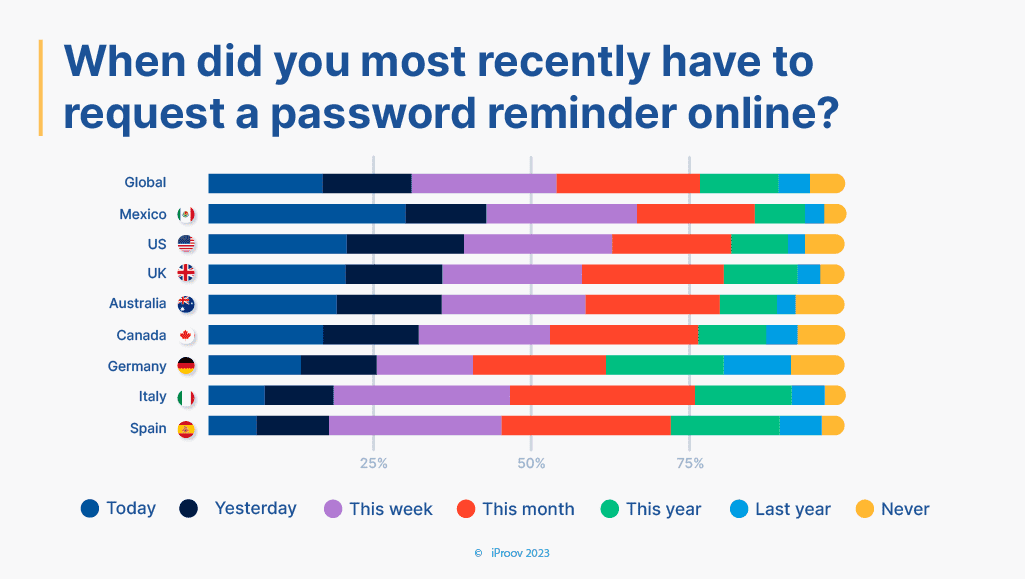
Let’s take a look at the statistics:
- 32% of global consumers have forgotten a password in the last 24 hours. This was highest in Mexico (44%) and lowest in Spain (19%)
- 74% of people have had to reset a password due to a data breach.
- Shockingly, 12% of people reported that they have reset their password 5 or more times because of data breaches.
It is difficult to protect the privacy of user data if the only thing standing between a fraudster and your customer’s data is a password. Clearly, they’re easily forgotten. Additionally, they have historically been undermined by large-scale data leaks and the availability of personally identifiable information on social media over and over again,
Biometric authentication replaces problematic knowledge-based authentication with inherence-based authentication. Trust is placed in who the person is, rather than the knowledge they can remember. Biometric data cannot be lost, stolen, or shared in the same way.
iProov’s biometric authentication systems have privacy built in by design to safeguard the user’s confidentiality, and strong encryption techniques protect all user data. Data is never shared with any third party and our security is exhaustively tested regularly by governments and enterprises.
It’s not just passwords. Traditional authentication methods, such as OTPs, have become commoditized in the wake of rapid digitalization. You can read more about the risks of OTP authentication here.
Ultimately, if data privacy is important to your organization – and you want to be seen as taking data privacy seriously – then passwords and other traditional verification technologies are unsustainable.
How Does iProov Ensure Data Privacy?
The truth is that iProov does not receive any biographical data (such as name, address, gender, date of birth) or even a phone number or email address. A firewall is in place so any and all end-user personal data that comes to us – including facial imagery and the resulting biographic template – is pseudonymized and cannot be associated by iProov with an identifiable person.
Several technological innovations are at play here:
- Biometric templates: A biometric template is a stored representation of biometric data. But it is not the data itself – it is biometric data that is then analyzed through various algorithms and mathematical models in order to convert that data into a biometric template. This generally means that stealing a biometric template would be useless for a fraudster. In iProov’s case, instead of imagery, the fraudster would find an anonymized binary code. Ultimately the template functions as a unique representation of the person, but it is not an image – ultimately bolstering user privacy and data protection.
- Privacy firewall: iProov’s technology uses a privacy firewall. iProov has no access to other information apart from the face, and the organization using iProov has no access to the biometric data. There is a structural separation between the user identity and the user biometric, which is highly effective in safeguarding the privacy of the user.
- Cloud-based authentication: There are many benefits to a cloud-based biometric security system over an on-device solution. One key one as it relates to privacy is the protection of user data: cloud security is opaque to an attacker and far more difficult to reverse-engineer. On the other hand, devices are far simpler to compromise, and when broken into provide access to the user’s identity – their image, their personal data, and access to their apps and services. Read more about cloud-based biometric security here.
Conformance and Compliance Highlights Commitment to Data Privacy
iProov delivers the most validated face biometric solutions in the world, having been exhaustively tested to national security and privacy standards by the U.S. Department of Homeland Security, the UK Home Office, the Singapore Government, and the Australian Government.
We comply with or conform to several key industry standards and regulations, providing our partners, customers, and future customers with the assurance that their data and users’ data are safeguarded properly by iProov.
- iProov is certified to SOC 2 Type II. This certification assures that iProov’s system is designed with suitable organizational controls to ensure sensitive information is kept secure in the cloud.
- iProov operates worldwide in compliance with the European General Data Protection Regulation (GDPR) and the UK Data Protection Act.
- iProov is ISO 27001 compliant and maintains this status continuously with annual audits. Importantly, the ISO certification scope covers the whole company, including all of the products and services it provides, controlled from iProov headquarters.
- iProov is certified under the European eIDAS regulation to Qualified Trust Service level and to eID Level of Assurance High.
- Other certifications include, but are not limited to: iBeta Level 1 and Level 2, ISO/IEC 30107-3, and ISO/IEC 19795-1:2006. iProov also complies with, and is externally audited against the iRAP standard.
You can see a list of our certifications here and learn more about conformance testing in our biometric encyclopedia.
If you’d like to discover how iProov can secure and streamline your organization’s online verification, authentication, and onboarding while meeting the most stringent of data privacy requirements, book your demo today