February 7, 2026
Think of the billions of users that enroll online every day for new digital services – subscribing to a streaming platform, taking out insurance, accessing medical records, opening a bank account. Organizations put enormous emphasis on onboarding as many customers as quickly as possible. More customers, more revenue. In the public sector, mass adoption of digital services is central to cost efficiency.
But what happens if you onboard a user who isn’t a real person?
Not someone pretending to be you – that’s traditional identity theft. This is different. This is someone who doesn’t exist at all. A fabricated person, assembled from fragments of stolen data, designed to look real enough to pass your checks, build a credit history, and then disappear with your money.
This is synthetic identity fraud. It costs businesses an estimated $20-40 billion globally per year. U.S. lenders faced $3.3 billion in exposure from synthetic identities tied to new accounts through 2024. And 44% of organizations now rank it as their top-tracked fraud type.
What makes it uniquely dangerous isn’t just the scale. It’s that there is no victim to report it.
What Is Synthetic Identity Fraud?
Synthetic identity fraud is the creation of a new, fictional identity using a mix of real, stolen, and fabricated information – then using that identity to open accounts, access services, or commit financial crime.
Unlike traditional identity theft, where a criminal steals and impersonates a real person, synthetic fraud creates a “person” who has never existed. That distinction matters enormously for detection, as we’ll explain below.
It generally takes one of three forms:
Identity fabrication: Built entirely from fictitious data. No genuine personal information is used.
Identity manipulation: Real identity data slightly altered – a changed digit in a social security number, a modified date of birth – to create a new identity that passes validation.
Identity compilation (Frankenstein fraud): Real data elements from multiple sources combined into one new identity. A legitimate social security number paired with a fake name and a stolen address. This is the most common and most dangerous form because each individual data point looks legitimate on its own.
The Invisible Victim Problem: Why Synthetic Fraud Breaks Traditional Detection
Here’s the structural issue that separates synthetic identity fraud from every other type of fraud: there is no real person monitoring the fraudulent activity.
In traditional identity theft or account takeover, there’s a real victim. They notice unfamiliar transactions. They call their bank. They file a report. The fraud gets flagged. Detection starts with the victim.
In synthetic identity fraud, nobody calls. Nobody reports. The identity was invented, so there’s no real person checking statements or monitoring credit. The fraud operates in silence – often for months or years – until the criminal decides it’s time to cash out.
This creates a cascade of problems for organizations:
- Fraud detection systems that rely on behavioral anomalies don’t trigger because the synthetic identity is the baseline. There’s no “normal” to deviate from.
- Credit bureau checks don’t catch it because each individual data element – a real SSN, a fabricated name, a plausible address – can look legitimate in isolation.
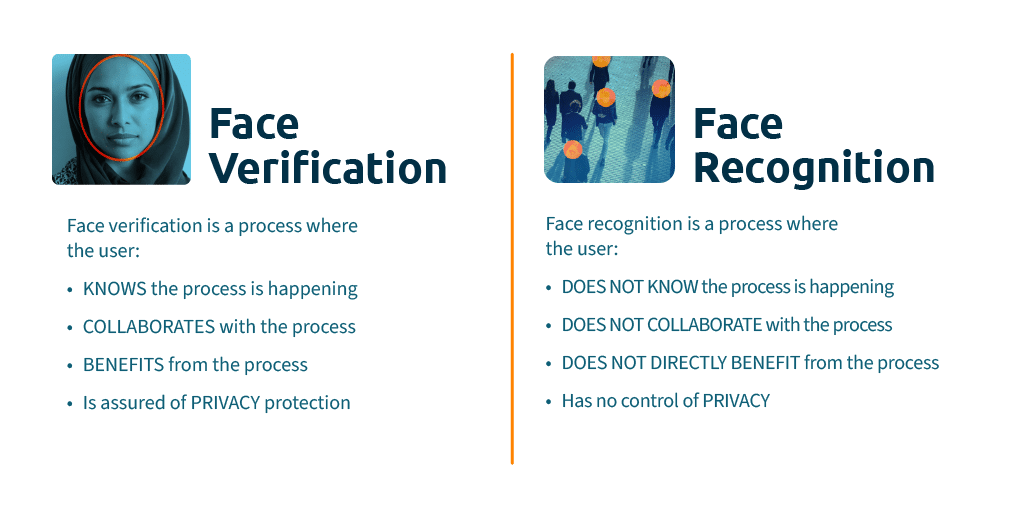
- Knowledge-based verification fails because any information that can be typed can be stolen or invented. This is why identity proofing must go beyond data matching.
- Recovery is nearly impossible because when the bust-out happens, the “person” who owes the debt doesn’t exist. Losses are written off as bad debt.
This is why synthetic identity fraud is structurally harder to stop than any other fraud type. The absence of a victim isn’t a side effect – it’s the feature that makes the entire scheme work.
Who Gets Hurt: The Hidden Victims of Synthetic Fraud
There may be no “visible” victim, but real people are harmed. The legitimate data fragments used to build synthetic identities have to come from somewhere – and they tend to come from the most vulnerable populations:
- Children: A child’s social security number has a clean credit history and won’t be checked by its owner for years, sometimes decades. It’s the ideal foundation for a synthetic identity.
- Deceased individuals: Records of deceased people are exploited because they won’t trigger activity from the real owner.
- Elderly individuals: Often have thin or dormant credit files and may not actively monitor their credit.
- Immigrants and people new to the credit system: Thin files and unfamiliarity with local systems make them prime targets for SSN theft.
When a child turns 18 and applies for their first credit card, they may discover their social security number has been building someone else’s credit score for years. The damage is real, even if the identity was fiction.
The Lifecycle of a Synthetic Identity Attack
Understanding how synthetic fraud unfolds over time reveals where defenses can intervene – and where most organizations currently have blind spots.
Phase 1: Identity Assembly
The fraudster constructs a synthetic identity by combining a legitimate identifier (typically a real SSN sourced from data breaches or the dark web) with fabricated personal details. The iProov Threat Intelligence Report 2025 documents how Crime-as-a-Service networks now sell identity assembly toolkits that automate this process at scale. Some fraudsters go further, building backstories for synthetic identities – social media profiles, professional histories, even small websites – to add credibility.
Where defense should happen: At the point of onboarding, before the identity ever enters your system. This is where biometric face verification with genuine presence detection is decisive – a fabricated identity has no real human behind it, so nobody can provide the biometric match.
Phase 2: Credit Cultivation
The synthetic identity is introduced into financial systems and patiently “nurtured.” Small accounts are opened, regular payments are made, credit limits increase. Over months or years, the identity builds a legitimate-looking credit profile. Some fraudsters add themselves as authorized users on real accounts to accelerate the process.
Where defense should happen: Continuous monitoring for behavioral patterns associated with synthetic identities – new accounts with unusually rapid credit-building, authorized user additions with no apparent relationship, thin-file applicants with suspiciously clean histories.
Phase 3: The Bust-Out
Once credit lines are sufficiently high, the fraudster maxes out every account, takes out every available loan, and disappears. The synthetic identity evaporates. There’s no real person to pursue. Synthetic identities were involved in 21% of first-party fraud cases detected in 2025, and bust-out schemes remain one of the most common methods for cashing out these fabricated profiles.
Where defense should happen: It shouldn’t have to. If genuine presence verification catches the fabricated identity at onboarding, this phase never occurs. Every dollar spent on bust-out detection is a dollar that should have been invested in onboarding verification.
Why Basic Biometrics Are Not Enough
Not all biometric systems defend against synthetic identity fraud equally. A basic face matching system that simply compares a selfie to a document photo can be defeated if the fraudster provides a matching deepfake image or uses a real person (an “identity mule”) to complete the verification before handing the account over.
This is why the type of biometric verification matters. Defending against synthetic identity fraud at onboarding requires three things simultaneously:
- Confirmation that the person matches the identity document – standard face matching.
- Confirmation that a real, living human is physically present – not a photo, mask, deepfake, or injected video.
- Confirmation that the verification is happening right now – not a replay of a previous session or a pre-recorded feed.
The first check alone is insufficient. All three together are what makes genuine presence verification the structural answer to synthetic identity fraud – because even the most convincing synthetic identity falls apart when a real human must be physically present to activate it.
How iProov Solves Synthetic Identity Fraud
iProov’s Dynamic Liveness verifies all three conditions in a single, passive interaction. Here’s what that means in practice against synthetic fraud:
- Flashmark defeats deepfake stand-ins. iProov’s patented Flashmark technology illuminates the user’s face with a unique, unpredictable color sequence during each session. The reflection is analyzed to confirm genuine presence in real time. Each session generates unique biometric data that expires immediately – it cannot be replayed, intercepted, or synthesized. This means a fraudster can’t use a deepfake, a pre-recorded video, or an AI-generated face to activate a synthetic identity. iProov is the first and only vendor certified to NIST SP 800-63-4 and the first to achieve CEN/TS 18099 Level High for injection attack detection. During 40+ days of accredited testing, no successful attack was established.
- iSOC catches what static systems miss. The iProov Security Operations Center (iSOC) monitors attack patterns across all customers, geographies, and platforms in real time. When new techniques for activating synthetic identities emerge – new deepfake tools, new injection methods, new mule recruitment patterns – iSOC detects them and deploys defensive updates globally, without waiting for the next software release.
- Cloud architecture keeps the defense hidden. All verification happens in the cloud, not on the device. This means the verification process can’t be reverse-engineered by studying the device, and it enables the real-time visibility that powers iSOC.
- Passive verification doesn’t punish real users. The process requires no head turns, nods, or spoken instructions. iProov is WCAG 2.2 AA and Section 508 compliant, with algorithms tested for equitable performance across age, gender, and skin tone. Completion rates are typically above 98%. Robust fraud prevention at onboarding doesn’t have to cost you genuine customers.
- Beyond Consumer Onboarding: Synthetic Identities in the Workforce
Synthetic identities aren’t just targeting banks and credit card companies. Operatives from OFAC-sanctioned nations have infiltrated over 300 companies using fabricated identities and deepfake filters to pass remote hiring processes. A fabricated employee gains access to systems, data, and funds – and the organization may never realize the person they hired doesn’t exist.
The iProov Workforce Solution Suite extends genuine human presence verification across the employee identity lifecycle – remote hiring, shared device access, step-up authentication, and account recovery – closing the same onboarding gap that synthetic identities exploit in consumer services.
The 2025 iProov Threat Intelligence Report documents the tools and techniques powering synthetic identity fraud today. Download the full report here.
To see how iProov stops fabricated identities at the point of onboarding, book a demo.
Synthetic Identity Fraud FAQ
Why is synthetic identity fraud so hard to detect?
Because there is no real victim to report it. The identity was fabricated, so nobody is monitoring the account for suspicious activity. Each individual data element (a real SSN, a fake name) can look legitimate in isolation. Fraudsters often nurture synthetic identities for months or years, building credit before executing a bust-out. Traditional fraud detection relies on victims reporting anomalies – synthetic fraud removes the victim entirely.
Who is most at risk of having their data used in synthetic identity fraud?
Children, deceased individuals, elderly people, and immigrants are disproportionately targeted because their social security numbers are likely to have thin or dormant credit files. A child’s SSN may be exploited for years before they’re old enough to discover the damage.
How does biometric verification prevent synthetic identity fraud?
Biometric face verification with genuine presence detection requires a real, living human to be physically present during onboarding. A synthetic identity has no real person behind it, so nobody can provide the biometric match. Advanced solutions like iProov’s Dynamic Liveness also defeat deepfakes and injection attacks that attempt to impersonate a fictional person using AI-generated imagery.
What is the difference between synthetic identity fraud and identity theft?
Identity theft involves stealing a real person’s complete identity. Synthetic identity fraud involves creating a new identity by blending real and fabricated data. The key difference is that identity theft has a victim who can report it; synthetic fraud often does not, which is why it can persist undetected for far longer.
What is the difference between synthetic identity fraud and new account fraud?
New account fraud is the broader category – it covers any case where a fraudster opens an account under false pretenses, whether using a stolen real identity or a fabricated synthetic one. Synthetic identity fraud is a specific and increasingly dominant form of new account fraud, distinguished by the fact that the identity itself was invented rather than stolen. Both exploit weaknesses in the onboarding process, which is why verification at the point of account creation is critical.
How is generative AI making synthetic identity fraud worse?
Generative AI tools have dramatically lowered the barrier to creating convincing synthetic identities. Fraudsters leverage technologies such as Generative Adversarial Networks (GANs) to create photorealistic deepfakes and AI-generated identity documents at scale. Attack-as-a-Service marketplaces sell these capabilities as ready-made toolkits. This means synthetic identities are more convincing and more numerous than ever, making genuine presence verification at onboarding an essential defense rather than an optional one.