
Why Accessible Biometric Authentication Matters – and What to Look for in a Liveness Provider

Deliver a Robust Risk-based Authentication Strategy When MFA Is Failing

Native Virtual Camera Attacks: The Invisible Threat to Remote Identity Verification
iProov Named “Trailblazer” in Groundbreaking Deepfake and Synthetic Identity Report

Scattered Spider Shifts to Airlines: What To Do Now

Enterprise-Grade MFA For Workforce: Simplified Security with iProov Biometrics & OIDC

Why the M&S, Co-op, and Harrods Ransomware Attacks Were Inevitable — And How to Stop the Next One

Biometric Security Must Be Actively Managed | Beyond Static Liveness
Age Verification vs. Estimation: Why Certainty Matters for Compliance

Honey, What? Your Face Isn’t Private, But Your Biometrics Should Be
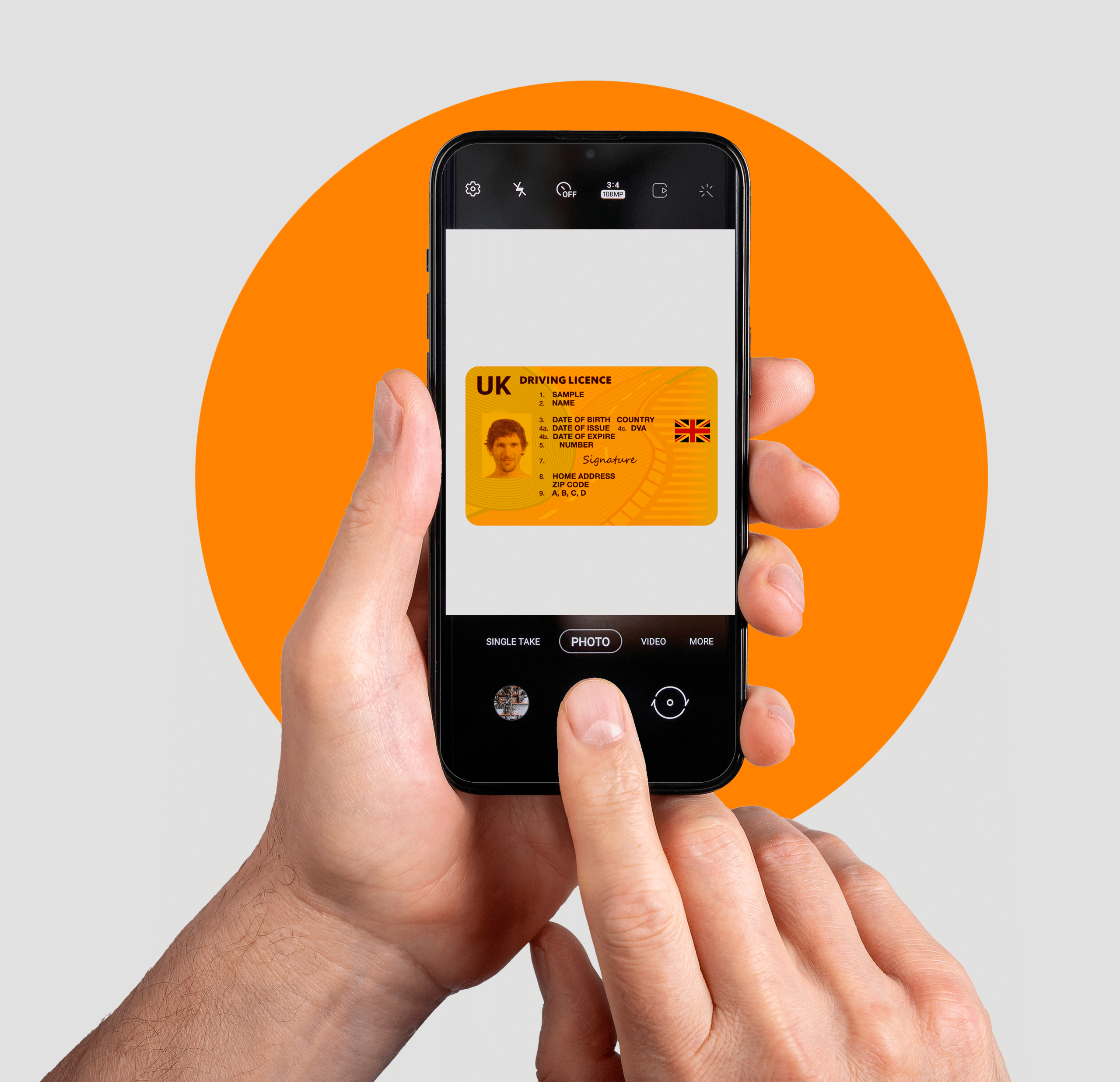
Document Verification Technology [Guide]: Making the Right Choice for Your Organization
New Account Fraud: How AI Is Changing the Threat and How to Stop It

The Critical Role of Identity Proofing in Digital Trust

Deepfake Fraud Is a Crisis – FinCEN Sounds The Alarm. Here’s How Financial Institutions Can Fight Back

The Top 5 Must-Read Analyst Reports of 2024 for Identity Verification and Cybersecurity Experts
Decoding Biometric Testing Frameworks and Certifications in the Age of AI Attacks
Get clear, expert guidance on how to evaluate biometric systems in the age of AI-driven identity attacks. Secure your spot today and stay ahead of evolving threats.
![20250709-[Project-ID]-Prism-Graphic-Animation-v1 |](https://www.iproov.com/wp-content/uploads/2025/07/20250709-Project-ID-Prism-Graphic-Animation-v1.gif)