November 20, 2023
In our last article in this series, “The Disadvantages & Vulnerabilities of Voice Biometrics | What’s the Alternative?”, we examined the limitations and vulnerabilities of voice biometrics – ranging from low assurance levels to security concerns and usability issues.
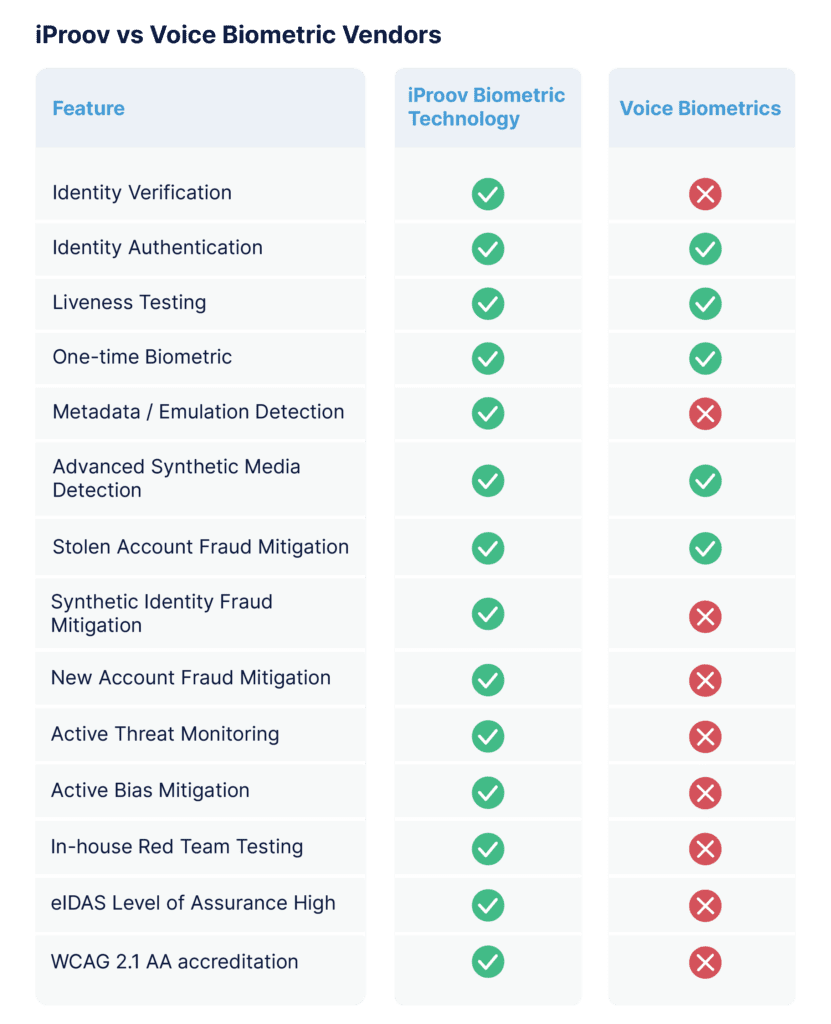
This article picks up where we left off. We’ll evaluate face biometrics as a secure and convenient alternative to voice biometrics. But the next question is crucial: how do you know which solution to trust?
To help navigate the challenge of identifying a trustworthy biometric solution, we’ll investigate the specific differentiators within verification technology – and explain the key factors to consider when making the leap from voice to face.
Key Business Drivers To Consider When Moving From Voice to Face
First, consider the leading factors that may be affecting your business’s key performance indicators (KPIs):
- Completion rates: The success rate of user verification is a critical driver for identity assurance technology. It is important to evaluate how many users can successfully complete the verification process, as this will vary between vendors and technologies.
- Security obligations and organizational reputation: Voice biometrics can cause breaches through false positive results or inadequate security – which often means significant reputational damage for organizations. With the rise in voice cloning technology, customers demand more reliable authentication alternatives.
- Regulatory and privacy compliance: Organizations operating in heavily regulated industries or jurisdictions may struggle to meet privacy regulations with voice biometrics. Evaluating alternative authentication solutions which better align with regulatory obligations and offer a higher Level of Assurance is critical.
When deciding to abandon voice biometrics, it’s important to conduct a comprehensive evaluation of the business drivers and assess how they align with your organization’s specific objectives and goals.
The right biometric face verification solution can enhance completion rates, security, and compliance in one end-to-end solution. With this in mind, let’s move on to the specifics.
Why Choose iProov Face Verification Over Other Biometric Options?
As we’ve established in the previous two articles, voice is not a reliable indicator of identity. It’s prone to spoofing, is difficult to obtain an authentic “source” to match against, and is prone to variance over time.
With face biometric verification, as with any remote identity solution, it’s crucial to evaluate the merits of the individual vendors and technologies, as not all technologies are created equal. iProov is trusted by some of the world’s most security-conscious organizations – such as UBS, The US Department of Homeland Security, and the The UK Home Office. Here’s why:
Level of Assurance
Level of Assurance (LoA) refers to the certainty you can have that an identity can be trusted to actually be the claimant’s “true” identity. The higher the assurance level, the more secure the identity and the lower the risk of successful attacks such as new account fraud, synthetic identity fraud, and identity takeover.
iProov has proved its LoA rating through certification from a number of leading LoA frameworks. For example, iProov is certified as a Trusted Service Provider (TSP) for biometric face verification of a natural person with Dynamic Liveness ‘GPA’ technology to the highest level of assurance in accordance with the eIDAS Regulation. Additionally eIDAS Module Certification as Trusted Service Service Provider (TSSP) for Electronic Identification (eID) and Electronic Signature (eSig) means we can provide trusted services to trusted service providers (TSP).
Whereas voice biometrics cannot even verify an identity – it can only authenticate it – iProov can verify and authenticate users with a Level of Assurance that meets the highest international standards for technology and business systems. This is a key competitive advantage and can reduce the associated cost and burden of implementation, auditing, and legal compliance for your business.
Certifications and Governance
Certification and governance accreditations are a market differentiator for biometric verification vendors. iProov’s Software Development Kit (SDK) conforms to many of the most stringent standards, for inclusivity, security, and privacy, including WCAG 2.2 – demonstrating online accessibility for all, regardless of age, literacy, language, cognitive ability, disability, or other constraints
All iProov solutions have been inherently designed for privacy, and the business is certified to ISO/IEC 27001 and SOC 2 Type II – demonstrating how we safeguard customer data and how successfully those controls are operating. Plus, iProov is one of the only companies named a SIF mitigation vendor by the Federal Reserve.
You can learn more about some of iProov’s long and distinguished list of certifications here.
Security Testing
iProov provides science-based biometrics which includes a multimodal approach to attack detection, testing both imagery and metadata to deliver a high level of assurance that a remote user is genuine. Our security has been evaluated by the best: external Red Team Testing (e.g., DHS, Outflank u0026amp; AIS); full accreditation by iBeta for Presentation Attack Detection to the standard ISO 30107-3; and continuous in-house Red Team Testing.
iSOC
Adaptability is critical for identity assurance technologies. The lag between the time an exploit is detected, processes are adapted, and security is redeployed presents a significant risk as the threat landscape constantly evolves. Therefore, organizations must remain vigilant and agile to ensure their systems are secure and resilient to evolving threats. Static on-premise security is outdated and ineffective.
iProov is the only biometric vendor with active threat monitoring in the cloud, enabling us to track threats, evolve, and respond in real-time. You can read about the importance of evolving and adaptive security here.
One-Time Biometric Technology
iProov delivers a unique one-time biometric technology, which verifies that an individual is authenticating in real-time and is not a photo or mask, nor a digitally injected attack using a replay of a previous authentication, or synthetic video (such as a deepfake). The user’s device screen illuminates their face with a unique sequence of colors that cannot be replayed or manipulated synthetically. It also analyzes multidimensional information derived from the way the face behaves and how light is reflected off of a face, which is key in uncovering synthetic imagery.
One-time biometric technology is essential to defend against the growing threat of fraud and synthetic media. iProov is completely unique in the identity assurance space, largely owing to its ability to confirm whether a device is sharing correct real-time information about a real user right now. It’s more than just a timestamp that can be easily manipulated – it’s a challenge-response mechanism, utilizing a science-based flashmark technology to ensure real-time authenticity.
Proven Experience Delivering at Scale with Industry Leaders
The iProov solutions are designed to be accessible, scalable, and resilient, with a high level of uptime and the capacity to handle millions of verifications. iProov has proven its ability to scale in real-world scenarios, with major deployments globally processing over 1 million verifications daily. iProov is a proven supplier, and financial services organizations such as Bradesco, Rabobank, and Knab already actively use and rely on it.
Making the Leap – Moving Away from Voice Biometrics
Overall, voice biometrics has fundamental and significant limitations and should only be deployed in low-risk scenarios. Voice is only suitable for use cases where the level of assurance required is low, and there’s already a lot of contextual data that the person is who they claim to be.
Biometric face verification has emerged as the most secure and convenient way to verify identity online, as traditional methods such as passwords and one-time codes have failed for high-risk use cases. Now, other inherence-based factors reveal cracks in their foundations – failing to defend against the growing threat of synthetic media and groundbreaking advances in generative AI.
With iProov’s combination of patented features, key certifications, and proven experience with industry leaders, your organization can confidently transition from voice to face biometrics, ensuring a secure, convenient, and inclusive verification and authentication process.
What happens when you transition to iProov?
- Initial consultation and setup: A dedicated team of solution architects and customer success professionals will be assigned to support you through your integration. You can expect an implementation kick-off and dedicated solution architect introduction immediately. While the iProov SDK has been designed to be very simple to set up, we know that each business has many additional complexities to consider, such as existing codebase and architecture, or regulatory environments to navigate – which is why we take a consultative approach. We have proven experience working through even the most complex integrations and we are well-versed in compliance and regulatory requirements
- In-depth, guided training: The iProov team will provide your teams training on the API or SDK of your choice (iOS, Android, Web, Cross Platform), iProov best practices, UI/UX guidelines, and on happy/unhappy path application logic – alongside handling setup and sharing necessary resources, documentation straight away. You can then expect further technical training tailored to your organization’s needs and use cases.
- Ongoing support and technical development: We’ll help you with customer app and iProov integration development support; iterative support and weekly progress touchpoints; end-to-end review, testing & and ongoing solution review and optimization, alongside continued support from your dedicated customer success manager.
If you’re ready to transition away from voice biometrics and enhance your authentication process with secure and convenient face verification – or if you’re interested in learning more about how iProov technology can benefit your organization – book your demo today. Our team will swiftly be in touch to provide the assistance you need.