
UK Cyber Action Plan 2026: What It Means for Identity Verification

APAC Races to Regulate Digital Identity & AI Amid Deepfake Surge

Deepfake Spoofs Dutch Bank’s KYC, Opening 46 Accounts. What Could Have Stopped It?

One Security Check Isn’t Enough: The Case for Multi-Layered Identity Protection
CEN/TS 18099: The Standard That Proves Injection Attack Resilience

Synthetic Identity Fraud: The Invisible Victim Problem and How to Solve It

Understanding Attack-as-a-Service: The Dark Ecosystem Fueling Identity Fraud
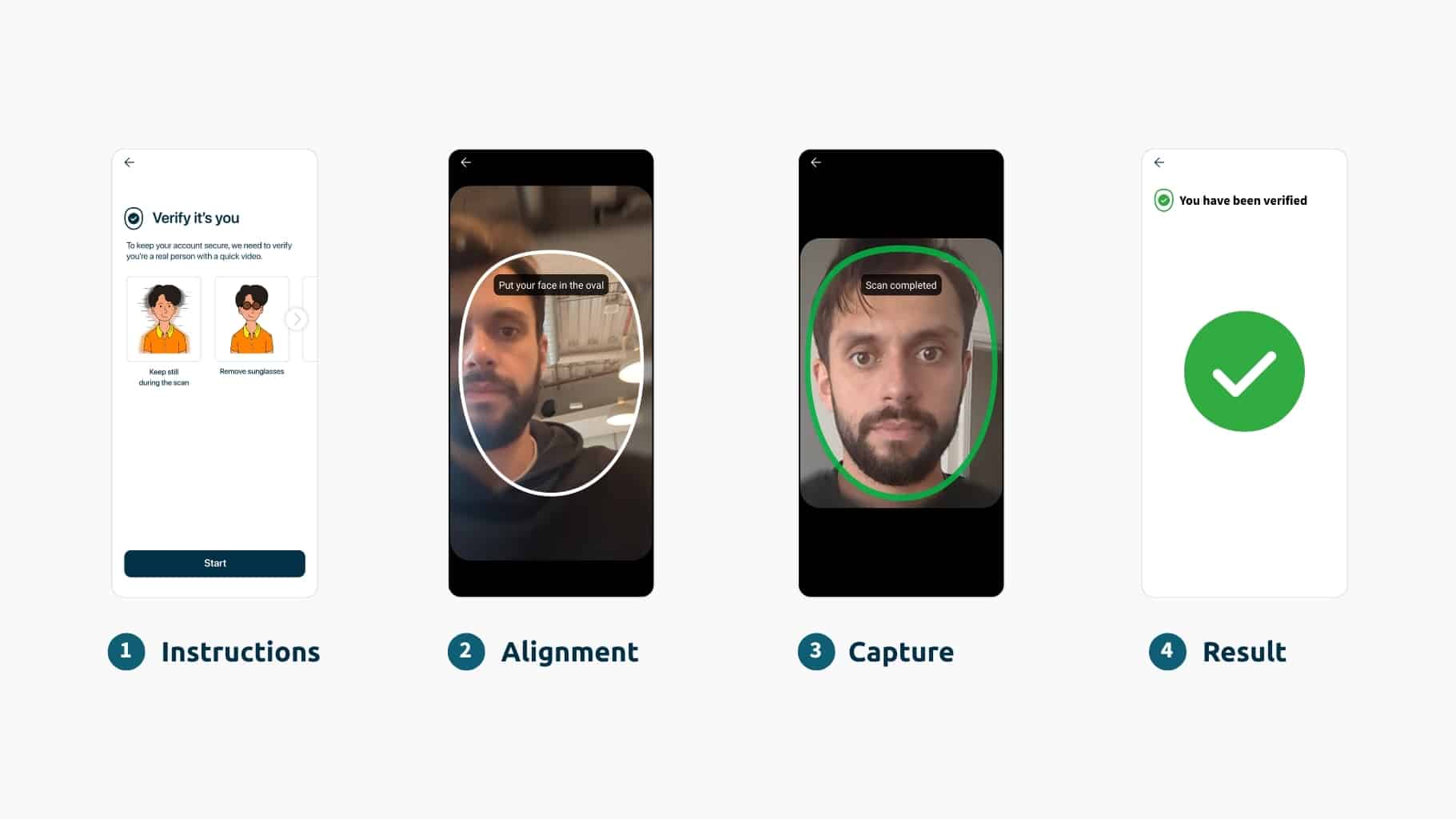
5 Common UX and Performance Challenges with Customer Face Verification (And How to Solve Them)

KYC vs AML: What They Mean, How They Differ & Why It Matters (2026)

The Numbers Don’t Lie: 80+ Biometric Statistics

What Is OTP Authentication? How It Works, Risks & Alternatives (2026)

NIST 800-63-4 Guidelines: An Identity Call To Action

The Trust Crisis Has Arrived: How AI is Accelerating Criminal Evolution

Biometric Vendor Evaluation: Inclusion, Bias, and Accessibility – What to Ask and What to Look For

Cryptocurrency Exchanges & Biometrics in 2026: Identity Verification Is Now Non-Negotiable
Webinar
AI-Driven Identity Attacks Are Already Inside the Enterprise. Are You Ready?
Join iProov on June 3rd at 10:00 AM EST / 3:00 PM GMT to learn how to protect your organization against the deepfake upside down. Register now