Interactive Threat Intelligence Experience
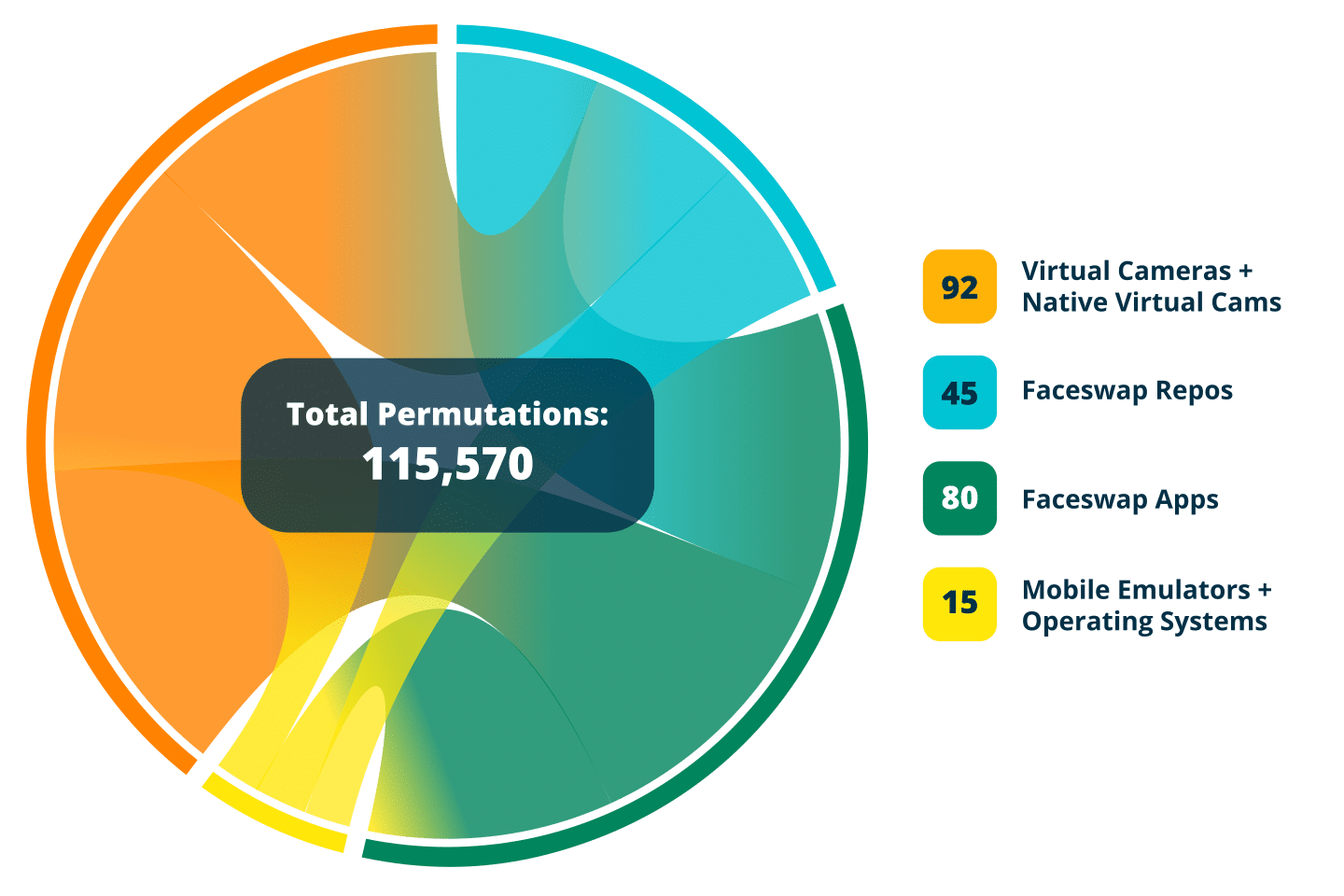
Explore this Interactive Threat Intelligence Experience: a dynamic, visual deep dive into the evolving world of remote identity threats and the defenses built to stop them. From face swaps and mobile emulators to virtual cameras and injection attacks, you’ll uncover how modern tools combine into over 100,000 unique attack permutations, and how real-time verification with Flashmark™ challenge-response helps detect and defend against them. Gain clarity, insight, and a new level of visibility into the threats facing your authentication systems.
Watch The Video: Explore Threats and Defenses Against Them
Threat Combination & Permutations Chart
Threat Intelligence Interactive Attack Vector Explorer
Can your verification methods withstand the rapidly shifting threat landscape?
This interactive experience maps the complete attack surface, examining how modern threat actors deploy digital injection attacks, adversarial machine learning, real-time deepfakes, replay techniques, and more. Each threat vector and user touchpoint represents a potential vulnerability that requires specific countermeasures.
Our interactive explorer breaks down the complete attack lifecycle, showing you exactly where vulnerabilities exist and how attackers exploit them.
Trusted By




CERTIFICATIONS MATTER.
- eIDAS Level of Assurance High
- ISO/IEC 30107-3
- SOC 2 Type II
- Certified G-Cloud Supplier
- Federal Reserve SIF Mitigation Provider
- iBeta
- iRAP
- UK National Physical Laboratory (NPL)