April 26, 2025
The threats to remote identity verification have fundamentally changed. What was once a challenge of detecting printed photos held up to cameras has evolved into an industrial-scale assault powered by generative AI, Crime-as-a-Service networks, and sophisticated digital injection tools.
Traditional authentication methods – such as one-time passcodes – are failing. Facial biometric verification has emerged as one of the most secure methods for organizations to verify user identity online. But not all biometric systems are equipped for the threats organizations face today.
Deploying biometric verification without visibility into how threats evolve is like building defenses without understanding what you’re defending against. To be effective, solutions must be resilient to the evolving threat landscape and actively managed – not simply resistant to known, established spoofs.
The Scale of the Threat: What The Latest Threat Intelligence Reveals
The iProov Threat Intelligence Report 2025, based on live observations of criminal activity worldwide from iProov’s Security Operations Center (iSOC), documents an unprecedented escalation in attack sophistication and scale.
Sharp increase in face swap, native virtual cameras, and digital injection attacks
- Native virtual camera attacks increased by 2,665% in 2024, becoming the primary threat vector as these tools infiltrated mainstream app stores.
- Face swap attacks surged 300% compared to 2023, with threat actors specifically targeting systems that use liveness detection protocols.
- Over 115,000 potential attack combinations are possible from just three common attack tools, underscoring why point-in-time testing is no longer sufficient.
- Only 0.1% of participants in an iProov study correctly identified all deepfake and real content, demonstrating that human judgment alone cannot defend against these threats.
These numbers represent a fundamental shift. Simple, lone-wolf attacks have evolved into a complex, multi-actor marketplace where sophisticated tools are bought, sold, and deployed by low-skilled actors at an industrial scale. You can read more about how this criminal ecosystem works in our analysis of Attack-as-a-Service networks.
Static Liveness Deployments Alone Are No Longer Enough
Liveness detection — confirming that a real, live person is present at the point of capture — remains essential. But it has become a baseline, not a differentiator. The threats that organizations face today go beyond what liveness alone can address.
The industry conversation has shifted. The question is no longer “do you have liveness detection?” It’s “can you prove the person is genuinely present at the point of capture AND defeat sophisticated attacks that bypass the camera entirely — and can you keep doing that as new attack methods emerge?”
This shift is now codified in two landmark standards:
NIST SP 800-63-4: The New U.S. Federal Standard
The U.S. National Institute of Standards and Technology released NIST SP 800-63-4 — the first update to its Digital Identity Guidelines since 2017. The new standard introduces specific controls for injection attacks and forged media, mandating that biometric systems at Identity Assurance Level 2 (IAL2) and above must implement presentation attack detection AND analyze media for signatures of AI-generated content and deepfakes.
iProov is the first and only biometric vendor independently certified to meet these requirements.
CEN/TS 18099: The Injection Attack Detection Standard
CEN/TS 18099 is the first testing standard specifically designed to evaluate biometric systems’ ability to detect and defeat injection-based threats. iProov Dynamic Liveness is the first and only solution to achieve CEN/TS 18099 Level High (Ingenium Level 4) — the highest tier of independent testing — following evaluation by ISO/IEC 17025-accredited Ingenium Biometric Laboratories.
During over 40 days of testing, no successful injection attack method was established against iProov’s system.
These certifications matter because they move the conversation from marketing claims to independently verified, lab-tested evidence. Learn more about iProov’s full certification stack here.
How Active Threat Management Defends Against Evolving and Unknown Threats
iProov’s defense architecture is built on three interconnected pillars. Each reinforces the others, and together they create a security model that no single capability alone can match.
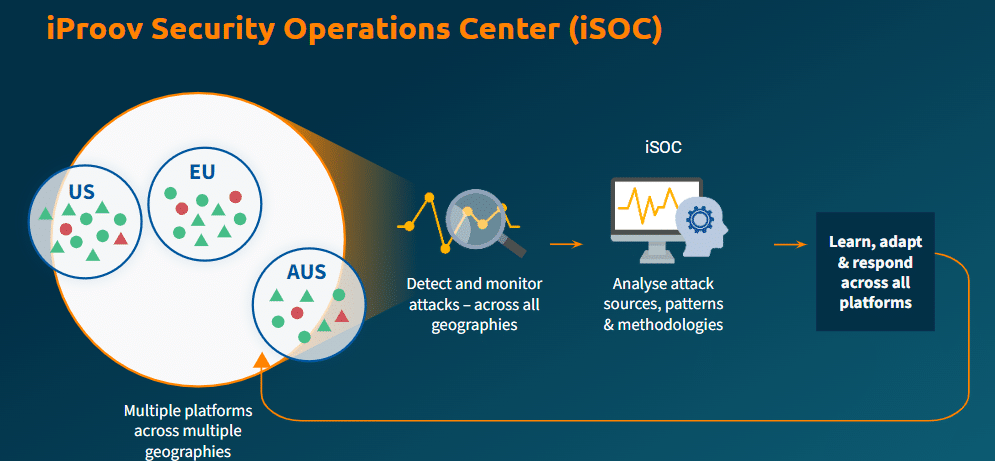
Pillar 1: iSOC — The Industry’s First Biometric Threat Intelligence System
The iProov Security Operations Center (iSOC) is the industry’s first global biometric threat intelligence and active threat management system.
Through iSOC, iProov monitors traffic in real time to detect attack patterns across all customers, geographies, devices, and platforms. This delivers continuous monitoring and learning from attack sources, patterns, and methodologies — keeping defenses ahead of the evolving threat landscape.
Why does this matter?
Once attack tools or methodologies successfully breach a system, they are rapidly shared — typically on the dark web or within Crime-as-a-Service networks — and can scale very quickly. Without visibility into how attacks are evolving, it becomes very difficult to prioritize defenses or understand how attacker behavior is changing.
Why can’t other vendors replicate iSOC?
No other biometric vendor operates anything comparable. The reason is architectural: to run a global threat intelligence operation on biometric attacks, you need three things simultaneously:
- Cloud-based verification — to see all traffic across all customers in real time.
- A large enough customer base across high-assurance sectors — governments, banks, border agencies — to observe diverse and sophisticated attack patterns.
- A dedicated science team — computer scientists, ethical hackers, and threat intelligence experts who translate raw intelligence into defensive updates.
Without all three, a vendor either lacks the visibility (on-premise models), lacks the attack diversity (small or single-sector customer base), or lacks the expertise to act on what they see.
iSOC delivers:
- Real-time detection: Attacks are spotted and investigated as they happen.
- Shared intelligence: Every customer benefits from attacks detected against any customer, across all geographies and sectors.
- Continuous adaptation: Security updates deploy globally without disruption to organizations or end users.
94% of organizations agree that a biometric security partner should provide an evolving service, not just a software product. iSOC is how iProov delivers that. Learn more about why evolving defense matters in the age of AI.
Pillar 2: Cloud-Based Verification as a Security Architecture
Cloud-based verification is not simply a deployment choice. It is an architectural security decision that enables capabilities impossible in on-device or on-premise models.
Verification happens in the cloud, not on the device. If an attacker manages to physically or digitally compromise a device — with ransomware, for example — the verification remains unaffected because it is separated from potential vulnerabilities on the device.
The cloud powers iSOC. iProov monitors and analyzes attacks in real time because verification happens in the cloud. This provides full visibility over the execution environment — something on-device solutions simply cannot achieve.
Updates deploy instantly. Cloud-based SDK deployment means security updates roll out server-side, without requiring devices to be patched manually. Defenses and algorithms evolve continuously, making life significantly harder for attackers.
An on-premise biometric system’s security is static the moment it ships. The threat landscape is not. Learn more about cloud vs. on-device biometric security.
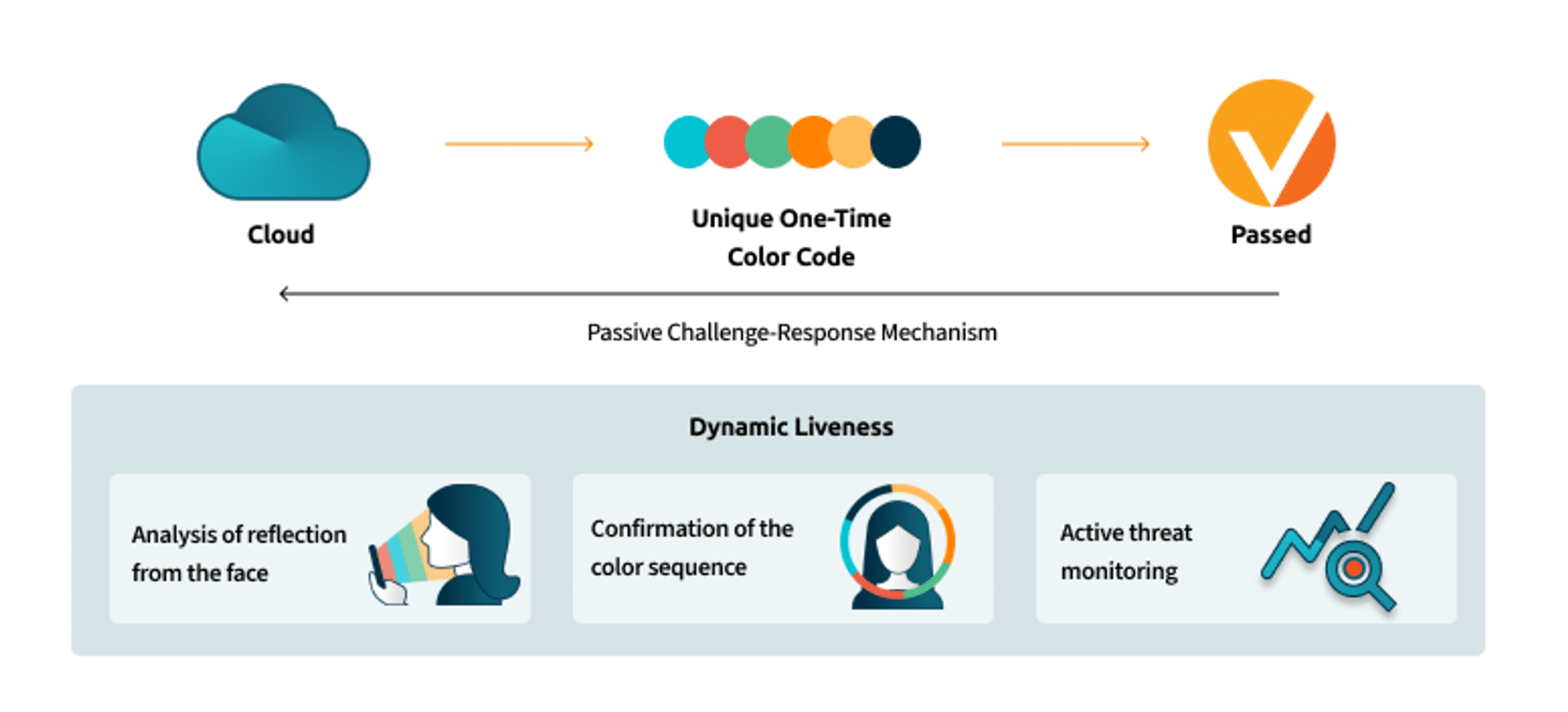
Pillar 3: Flashmark — Unique Per-Session Biometric Data
iProov’s patented Flashmark technology sends a unique, unpredictable sequence of colors to the user’s device screen during each verification session. The reflection of this light sequence from the user’s face is analyzed to confirm that the person is genuinely present — a real, three-dimensional human being, verifying right now.
How does this work? The color sequence that reflects from the face must match the sequence the device was instructed to display. If the imagery looks realistic but the color sequence is wrong, the system identifies a spoof. Because each sequence is unique and expires immediately after use, it cannot be replayed, intercepted, or pre-recorded.
This mechanism is entirely passive — no head turns, nods, blinks, or spoken instructions are required. The user simply looks at the camera, and the process completes in seconds.
This matters for two reasons:
- Security: Each session generates unique biometric data that is worthless if stolen, because it can never be reused.
- Inclusivity: Passive verification avoids the accessibility barriers created by active challenges. iProov is WCAG 2.2 AA and Section 508 compliant, with algorithms trained on balanced datasets and tested in production for performance across age, gender, and skin tone.
The Three Pillars Working Together
These three components form a single integrated architecture. Flashmark generates unique per-session data. Cloud-based verification processes it in a tamper-resistant environment and gives iSOC real-time visibility. iSOC detects emerging patterns and pushes defensive updates to all customers simultaneously. This feedback loop – detect, analyze, adapt, deploy – is what makes iProov’s security evolving rather than static.
This ultimately helps to protect your users and your organization from future and as-yet unknown threats. And, best of all, it’s all handled for you as an ongoing service.
The Cost of Getting This Wrong
A single deepfake video call cost Arup $25 million in fraudulent transfers. Operatives from OFAC-sanctioned nations have infiltrated over 300 companies using deepfake filters to pass remote video interviews. 62% of organizations experienced a deepfake attack in the past year.
The question for any organization using biometric verification is not “can we afford the most resilient defense?” It’s “can we afford to be wrong?”
iProov’s biometric solutions are trusted by the organizations where the answer to that question carries the highest stakes: the U.S. Department of Homeland Security, the UK Home Office, GovTech Singapore, the Australian Taxation Office, ING, UBS, and ID.me.
The 2025 iProov Threat Intelligence Report provides exclusive insights into the attack methodologies, tools, and threat actors observed by iSOC. Download the full report here.
To learn how iProov can defend your organization against the evolving threat landscape, book a demo.